In today’s digital landscape, mysterious codes and technical identifiers often circulate online, promising enhanced performance, hidden features, or exclusive system access. One such keyword that has recently gained attention is “how to use 35-ds3chipdus3 code.” At first glance, it appears to be a legitimate technical string, possibly associated with firmware configuration, device optimization, or software activation. However, as with many obscure digital terms, understanding its purpose requires a deeper and more careful evaluation.
This article explores the 35-ds3chipdus3 code in detail, examining what it is believed to represent, how it is claimed to work, and whether it has any real-world application. By focusing on clarity, accuracy, and practical insight, this guide aims to help readers navigate the confusion surrounding this code while avoiding common pitfalls and misinformation. 35-ds3chipdus3
Understanding the Structure of 35-ds3chipdus3 Code
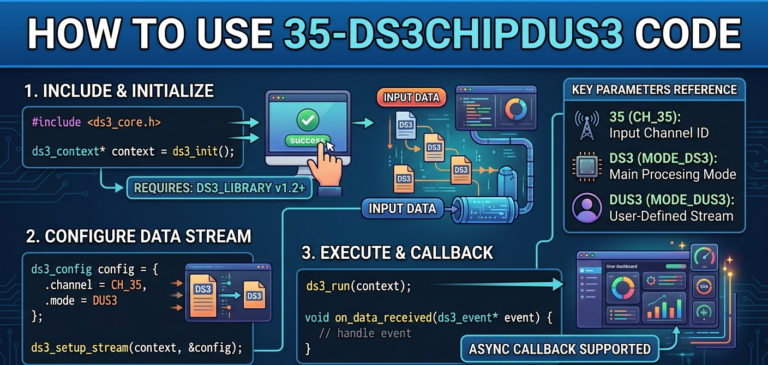
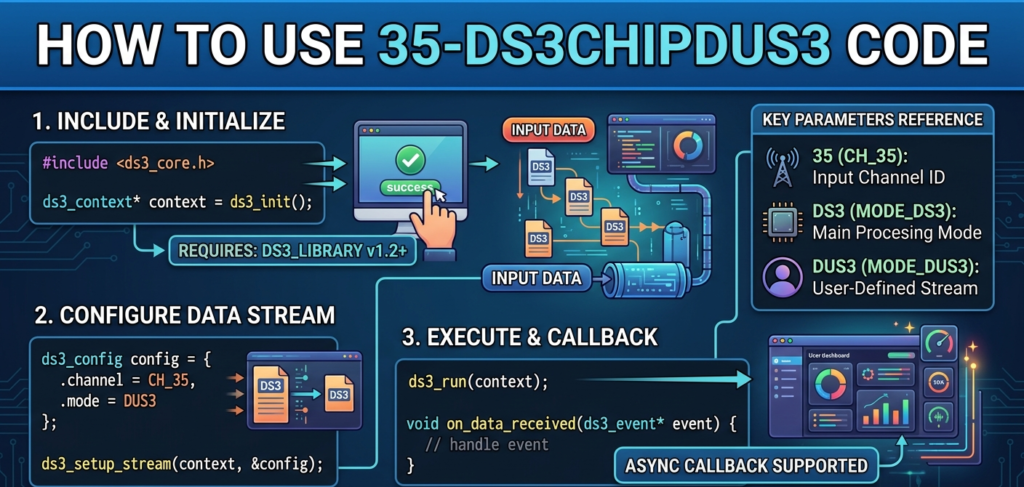
The 35-ds3chipdus3 code follows a pattern that resembles technical identifiers commonly used in computing systems. The combination of numbers and letters gives the impression of a structured naming convention, similar to firmware IDs, chipset references, or internal configuration keys used by developers and manufacturers.
The first segment, “35,” is often interpreted as a version number or product series indicator. In many real-world systems, numerical prefixes are used to define a generation or release category. The middle portion, “ds3chip,” appears to reference a chipset or hardware component, suggesting a connection to system-level operations. The final segment, “dus3,” is commonly assumed to represent a variant, region-specific identifier, or security token used to validate access.
Despite this seemingly logical structure, there is no confirmed documentation linking this code to any official hardware or software system. Its format may mimic genuine identifiers, but that alone does not confirm authenticity.
Why This Code Is Trending Online
The growing popularity of the 35-ds3chipdus3 keyword can be attributed to how digital content spreads across the internet. Technical-sounding phrases tend to attract attention, especially among users searching for solutions related to device performance, activation codes, or system upgrades.
Many websites publish content around such keywords to capture user interest, even when the underlying topic lacks real substance. As more pages reference the same term, it creates an illusion of legitimacy. Readers encountering multiple articles about the same code may assume it is widely recognized or officially supported.
This cycle of repetition often leads to confusion. Instead of providing verified information, the content simply echoes similar assumptions, making it difficult for users to distinguish between factual knowledge and speculation.
Claimed Functions and Uses of the Code
Various online discussions suggest that the 35-ds3chipdus3 code can be used during installation processes or system configuration. It is often described as an activation string that unlocks advanced features or enables compatibility between hardware and software components.
Some sources claim that entering the code into a specific field during setup allows the system to recognize certain modules or optimize performance settings. Others describe it as a bridge between firmware and applications, helping devices run more efficiently or access hidden capabilities.
While these explanations sound plausible, they are not supported by any credible technical documentation. Without official confirmation, these claimed uses remain theoretical and should be approached with caution.
The Supposed Mechanism Behind Its Operation
According to various descriptions, the 35-ds3chipdus3 code is intended to function as a unique identifier within a system. When entered correctly, it is said to trigger a sequence of operations that validate the user’s access and enable specific features.
Some explanations go further, suggesting that the code is divided into segments that perform different roles. One part may handle initialization, another may manage execution, and a third may verify system compatibility. This modular concept aligns with how real-world systems sometimes process configuration inputs.
However, without any official framework supporting these claims, the mechanism remains speculative. In practice, using unknown codes rarely produces meaningful results and may instead lead to system errors or failed configurations.
Common Misunderstandings Surrounding the Code
One of the most widespread misconceptions is that the 35-ds3chipdus3 code acts as a universal solution for unlocking features across multiple platforms. Many users believe that entering this code can instantly improve performance or grant access to restricted functionalities.
Another misunderstanding is the assumption that the code represents a real chipset or firmware component. While its structure may suggest a technical origin, there is no evidence linking it to any recognized product or manufacturer.
It is also important to note that repeated mentions of a term do not confirm its validity. The presence of multiple articles discussing the same code often reflects content duplication rather than genuine verification.
Risks Associated With Using Unverified Codes
Attempting to use unknown or unverified codes can introduce several risks. One of the primary concerns is system security. Entering arbitrary codes into software or hardware interfaces may expose vulnerabilities or lead to unintended behavior.
Another potential issue is system instability. Incorrect inputs can disrupt normal operations, causing errors, crashes, or compatibility problems. In some cases, users may experience data loss or reduced performance after applying unsupported configurations.
There is also the risk of encountering misleading or harmful content online. Some sources promoting such codes may direct users to unreliable downloads or unsafe platforms, increasing the likelihood of security threats.
Practical Alternatives and Safer Approaches
Instead of relying on questionable codes, users should focus on proven and reliable methods for system configuration. This includes using official activation keys, verified firmware updates, and trusted software tools provided by manufacturers.
Accessing documentation from legitimate sources ensures that any changes made to a system are both safe and effective. It also helps users understand the proper procedures for installation, configuration, and troubleshooting.
Taking a cautious and informed approach not only protects devices but also improves overall performance and reliability. By prioritizing authenticity and verification, users can avoid unnecessary risks.
Expert Perspective on Digital Codes
In professional environments, digital codes and identifiers are carefully designed and documented. They serve specific purposes, such as authentication, configuration, or system integration, and are always supported by clear guidelines.
Legitimate codes are typically distributed through official channels and are tied to specific products or services. They come with detailed instructions and are backed by technical support, ensuring that users can apply them correctly.
In contrast, codes like 35-ds3chipdus3 lack these essential characteristics. The absence of official documentation and consistent explanations suggests that they are not part of any recognized system.
Conclusion
The topic of “how to use 35-ds3chipdus3 code” highlights the challenges of navigating information in the digital age. While the code appears technical and promising, there is no verified evidence supporting its existence or functionality in real-world systems